Author: nicola.coen@vansonbourne.com
Navigating AI: UK Leaders Address Regulation, Relevance, and Risk
The latest results of Vanson Bourne’s ongoing AI B2B research series, based on insights from the Vanson Bourne Community, are in. Among them are quite a few findings that speak to UK leaders’ current AI concerns of the AI revolution. There are almost no aspects of AI that, in one form or another, businesses aren’t struggling to get to grips with.
Here are three key themes:
“Reg-u-lation time, come on!”
Seven in ten respondents to our March survey signalled that they need help preparing for AI regulations, such as the EU AI Act. The act is part of a broader EU strategy to ensure that AI systems are safe, lawful, and align with fundamental rights.
What’s particularly interesting about this statistic is twofold. These are UK respondents and the UK doesn’t even have its own AI Act. But there’s no doubt that aside from anything homegrown, business and IT leaders in the UK are fully aware of the implications for them of regulations originating across the Channel, such as GDPR.

If you’re a technology vendor currently extolling the virtues of your AI-centric solutions, ask yourself how well developed your organisation’s position is regarding the evolving regulatory environment. And how effective you are at communicating that position to the market. Vanson Bourne’s recent report on marcomms effectiveness would suggest the answer to be “not very”. And yet your audience cares … a lot.
Desperately seeking DeepSeek
In January, DeepSeek took the AI world by storm. It literally came from nowhere. Challenging the incumbent AI vendors and forcing us all to rethink whatever preconceptions we might have had about the future of AI.
In the last third of January, it was THE most talked about AI vendor. Building on this platform, by March it was … nowhere.

Whether or not DeepSeek makes a return or is eclipsed by the Next Big Thing, who knows? But that’s not the question we should be asking. The question we should be asking is: what impact has this had on the way that enterprise IT views the investment case for AI?
AI in cybersecurity: the poacher and the gamekeeper?
AI has the potential to enhance productivity, automate tasks and accelerate innovation. For all of us. And when I say “all of us”, I mean cyber criminals too. Nobody is excluded.
Cybersecurity is an arms race. IT decision makers are looking to vendors to deploy sophisticated AI solutions to counter … the sophisticated AI solutions being deployed by cyber criminals. And around half of our respondents are of the view that the criminals are winning.

But until AI grows a conscience, fighting fire with fire is all we have.
The AI Barometer
Each month we survey 100 IT and business leaders across the UK, from our expert network: the Vanson Bourne Community. We explore their AI plans, perceptions, priorities and pain points in their organisations and industries. From emerging trends to current concerns, we investigate what UK leaders are really thinking and doing when it comes to AI strategies and investment.
Explore more insights in a selection of recent articles and reports below:
- More players, more pressure? How the AI market is being shaken up
- Why building trust should be a top priority for AI vendors in 2025
- AI: The race for a use case
Exploring the 2025 Mainframe Landscape
This blog is in collaboration with:

Last year marked the mainframe’s 60th anniversary, a milestone that serves as a timely reminder of its endurance. But this isn’t about nostalgia. Our findings show the mainframe remains highly relevant today: 98% confirmed their organisation depends on the IBM mainframe to execute key functions. Neither is this reliance waning, an overwhelming 99% indicated they expect to continue depending on this technology well into the future.
However, the mainframe environment is not without its challenges when it comes to using it as a development and delivery vehicle. Almost all (96%) organisations report difficulties in the development and testing process. Our research highlighted these issues span a broad spectrum of operational pain points. Concerns include a lack of cost efficiency (39%), inflexibility (39%), debugging difficulties (38%), sustainability challenges (38%) and struggles to meet regulatory and compliance requirements (33%). Organisations clearly recognize these concerns, acknowledging them as both critical to their operations and in need of improvement.

Nearly four in five (79%) organisations express concerns that staffing limitations could hinder their ability to achieve core business objectives. The biggest skill gaps are in the more traditional mainframe technologies: only a third or fewer rate their teams as having a good skill/knowledge level in ISPF 3270 (33%), Assembler (29%), or REXX (27%). Without modern tools, many (83%) face difficulties recruiting and retaining the next generation of talent.
Organisations are seeking modern solutions that deliver a balance of flexibility, control and sustainability, without increasing costs. One approach to this is expanding mainframe environments: enabling efficient, scalable, and risk-conscious growth, and helping organisations to remain agile through constant change. Notably, over a third (34%) report an urgent need for additional environments to meet the demands of mainframe delivery.
What initiatives would our respondents prioritise if they could deliver mainframe deliveries faster?


Over half (53%) believe that modernising their mainframe capabilities could significantly help resolve skill gaps and improve talent attraction and retention. Other key benefits include:
- Increased agility/flexibility (58%)
- Easier regulatory and data compliance (52%)
- Accelerated innovation (51%)
- Quicker implementation of changes/deliveries (46%)
- Delivering IT-related sustainability objectives (43%)
- Improved cost efficiency (42%)
Mainframes remain mission critical platforms, delivering immense value for the organisations that rely on them. However, as business demands and technology continue to evolve, so too must the mainframe. Organisations that proactively invest in more agile and scalable mainframe environments are likely to be better equipped to navigate operational challenges, drive innovation and attract the new generation of talent.
Derek Britton, CMO at PopUp Mainframe, commented “As a mainstay of high-stakes enterprise computing, the mainframe is a powerhouse production server – but it needs to do more and more to support future needs and can be hampered by a range of factors. At PopUp Mainframe, we wanted to learn the details of what’s blocking mainframe teams from accelerating their output. Vanson Bourne have helped us unearth a range of genuine, topical insights from the mainframe market.”
Note on this research: The research included 175 senior decision-makers in DevOps and IT roles across a wide range of sectors, comprising financial services, insurance, retail, transportation, logistics, IT services, energy, media, leisure, and entertainment. Their organisations had to be using the IBM mainframe and have a minimum of 500 employees, representing both the US (100) and the UK (75).
Hybrid working
Breaking the Silence: Women in tech share what’s shifted—and what still needs to change
In January 2025, US President Donald Trump signed executive orders dismantling DEI programs within the federal government. This prompted giant tech corporations such as Google and Amazon to follow suit and roll back their own DEI policies. While this obviously impacts far more than just women in isolation, it does exacerbate challenges for a group who have traditionally struggled to enter and advance within the tech industry.
For International Women’s Day 2025, we spoke with three women working in tech today—a Chief Information Officer (CIO) leading a global team; a Program Manager navigating the complexities of enterprise technology; and a Major Incident Manager who transitioned into tech from engineering. Their voices share a powerful journey of resilience, advocacy, and progress—while highlighting the work still needed to achieve inclusivity in the industry.

Hurdles for women in tech today
According to a 2023 study conducted by ‘Women in Tech’, women made up around 26% of the population working within the IT sector. While significantly higher than 20 years’ previously where it is estimated that 9% were female, this stat still represents an industry dominated by men. The CIO we spoke to highlighted how, at her current level, she is often the only woman in the room. She has also faced gender bias first hand—with multiple assumptions throughout her career that she’d be the one making tea.

This was echoed by others, pointing out that while entry-level opportunities for women in tech are improving, middle management remains a bottleneck. The CIO adds to this from her experience: “Up to a certain mid-level career, there was an even distribution of men and women. But in the higher levels, it was a much lower percentage. The assumption that everyone went off to have families was completely untrue. [I attended a diversity and inclusion event where it became clear that] many women left at this stage because of the lack of promotion opportunities at senior levels”.
The major incident manager described her experience in male-dominated meetings, where women’s perspectives can sometimes be dismissed or overlooked. The challenge, she noted, isn’t just about getting a seat at the table, it’s about ensuring that voice is heard and valued.

Workplace culture: Moving beyond performative inclusion
Diversity initiatives have become a focus for many organisations over the past few years, but the women we spoke to emphasised the need for authentic inclusion rather than box-ticking exercises.
The major incident manager shared how some diversity programs can unintentionally create fatigue and resentment if they are not integrated into the company’s core culture. Inclusion isn’t about positive discrimination—it’s about ensuring merit, opportunity, and fairness for all employees.

The power of representation and sponsorship
One of the strongest themes that emerged in our discussions was the need for mentorship and particularly, sponsorship in order to support women in the tech field. Mentorship provides guidance and support on the job, but sponsorship is critical to actively opens doors for career progression. The CIO pointed out that her career growth was significantly influenced by sponsors—senior leaders who advocated for her, recommended her for leadership roles, and helped her navigate workplace politics:
The program manager believes that having women in leadership roles creates a ripple effect, encouraging more women to push forward in their careers. But she still sees middle management as very male-dominated with many women operating in junior entry level positions, and a few who’ve made it to the C-suite. And according to a 2022 report from McKinsey, just 52 women in tech are promoted to managerial positions for every 100 men. Plenty more can be done to support women in technology with furthering their careers, and it starts with representation.
But beyond just having female representation at the top, companies need to actively invest in development programs, mentorship initiatives, and sponsorship structures that help women advance into senior positions.
Looking ahead: A future built by women in technology
Despite the challenges, all three women we spoke to are optimistic about the future. There is a growing number of women entering cybersecurity, AI, and data science, and companies are beginning to recognize the value of diverse teams in driving better business outcomes.
There is plenty more that can be done by corporations and governments alike. Tech Education in schools should receive greater funding, as well as additional emphasis on apprenticeships and more advanced opportunities.

And their advice for women entering the industry?
Be vocal about your ambitions, build strong networks, and don’t be afraid to push yourself outside of your comfort zone.
This International Women’s Day, let’s celebrate not only the achievements of women in tech but also their role in driving meaningful change.
Emerging IT Trends
Wellbeing in 2025
What social media do IT decision makers use?
Rebuilding trust after a crisis
The Microsoft Outage: A Wake-Up Call for CrowdStrike and IT Security Vendors
The July 19th Microsoft outage, caused by a software update issue from cybersecurity firm CrowdStrike, likely feels like a distant memory to many. Most organizations affected by the outage were able to recover quickly, with 82% of respondents in our expert network, the Vanson Bourne Community, reporting that they were back online within a working day. But what about CrowdStrike? What long-term impact did this have on their reputation and brand? And what lessons can other companies learn from this incident in case they face similar challenges?
Is There Such a Thing as Bad PR?
On one hand, the outage might have inadvertently turned CrowdStrike into a household name. Before July 19th, ask someone on the street what CrowdStrike did, and you’d likely get a blank stare. Ask them after the incident, and you might hear something like, “That’s the company that broke the world.” In one dramatic moment, CrowdStrike became a globally recognized brand.
On the other hand, this incident has also been a significant blow. The company’s share price dropped by 32% in the 12 days following the outage. They are now facing lawsuits from investors and Delta Airlines passengers, with Delta itself threatening legal action for a $500 million loss linked to the disruption. Additionally, 74% of respondents in our Vanson Bourne Community survey reported having lower trust in CrowdStrike after the incident. More than two-thirds (68%) are now less likely to recommend CrowdStrike as a cybersecurity provider.
So, how can CrowdStrike—and other brands facing similar crises—recover from this? What long-term effects will this have on their business and client relationships? And most importantly, how can they rebuild trust?
The Critical Role of Trust in IT Vendor Relationships
Trust is everything when it comes to selecting technology vendors, especially in the cybersecurity space. Our research shows that trust and reputation are often more important than price for our Community members when making vendor decisions. Trust is built over time through performance, personal relationships, and how a vendor responds in a crisis. If a vendor fails to respond effectively to a challenge, or doesn’t learn from its mistakes, it risks irreparably damaging the relationship.
How Can CrowdStrike Rebuild Trust?
- Immediate and Clear Communication
Clear communication during and after a crisis is critical. As one of our Community members pointed out, “Nothing is more frustrating than a delayed flight, especially when you don’t know when you’ll take off.” Similarly, during an IT failure, what matters most is understanding what’s happening, what’s being done to fix it, and when the issue will be resolved.
CrowdStrike’s crisis communication during the July 19th outage received mixed reviews. Some felt that the updates were insufficient and overly technical, leaving many customers confused and frustrated. In hindsight, it seems the communication window may have already passed for CrowdStrike. But is it too late? Perhaps not entirely.
- Transparency and Accountability
Transparency is essential after a crisis. Customers want to know that their vendor acknowledges the problem and owns up to the mistakes. CrowdStrike took a step in the right direction when its President Michael Sentonas accepted the “Most Epic Fail” award at Def Con in August. This public acknowledgment was a rare but commendable move that helped rebuild some goodwill.
But transparency shouldn’t stop there. CrowdStrike will need to ensure that they are not only admitting mistakes but also learning from them. This includes conducting a thorough ‘lessons learned’ review and communicating the remedial actions taken to prevent a recurrence. Clients need to feel reassured that this won’t happen again.
- Demonstrating Improvements
CrowdStrike has already outlined several actions aimed at preventing future issues, including improving its testing processes and staggering update rollouts. However, it will take time for clients to see the effectiveness of these measures in action. The real challenge will be demonstrating that these improvements are not just lip service but are having a tangible impact on service quality.
Measuring the Impact of a Crisis: Brand Research
For CrowdStrike, and any other brand facing a crisis, it’s important to measure the impact of the event on their reputation and relationships with clients. This is where brand research can play a crucial role. By tracking brand perception over time, companies can benchmark the impact of a crisis and adjust their response accordingly.
Effective brand research doesn’t just focus on a single metric. It should provide a holistic view of how a crisis affects different stages of the customer journey—from awareness to consideration—and how perceptions of key brand attributes, like trust, may shift in response. This information is invaluable for informing future positioning, messaging, and crisis management strategies.
For example, brand research can help organizations identify:
- Changes in awareness following a crisis.
- Shifts in customer trust and perception.
- How the event affects customer loyalty and likelihood to recommend.
By understanding these dynamics, brands can adapt their strategies to better engage their customers and recover quickly after a crisis.
What’s Next for CrowdStrike?
It’s clear that CrowdStrike has a long road ahead in terms of rebuilding trust and restoring its reputation. However, by embracing transparency, accountability, and continuous improvement, they have a chance to recover and even come out stronger. Ultimately, it’s the actions they take now that will determine the long-term impact of this crisis on their business and their relationships with customers.
For other brands facing similar challenges, this is a reminder of the importance of crisis management, open communication, and having a solid framework for learning and improving from setbacks.
100 IT decision makers from the Vanson Bourne Community were interviewed in the UK in August 2024. All came from organisations across a range of sizes and private and public sectors. As a member of the Vanson Bourne Community you’ll gain access exclusive to a variety of insights reports just like this one, based on research with our members. Sign up for free here.
Staying one step ahead: Leveraging market insights for identity and access management
Understanding the Evolving Threat Landscape
The recent Snowflake credential breach, which impacted over 150 organizations, serves as a stark reminder of the critical role that Identity and Access Management (IAM) plays in defending against increasingly sophisticated cyber threats. This incident underscores a key truth: no organization, regardless of size or industry, is immune to cyber risks.
To stay one step ahead of these threats, it’s essential for organizations to embrace a proactive approach to security. As the saying goes, “hackers don’t hack in; they log in.” Robust IAM solutions are a must—but they must be informed by data and strategic insights. This is where market research becomes invaluable, offering organizations the intelligence they need to anticipate future threats and outperform competitors.
Methodology: Blending Quantitative and Qualitative Approaches
Our approach to uncovering meaningful IAM insights combined both quantitative and qualitative research methods. While quantitative data provides solid numbers that can track trends and inform decisions, the real power comes from the qualitative insights—gathering feedback directly from IT decision-makers to understand their challenges, priorities, and pain points.
By starting with qualitative research, we were able to dive deeper into the experiences and perspectives of industry professionals. These insights then guided our quantitative phase, enabling us to focus on the most relevant topics and generate more actionable data. This blended methodology gave us a 360-degree view of the IAM landscape, with both in-depth analysis and reliable metrics, ensuring our findings were both robust and credible.
Key Findings
Security is a Top Priority — Yet Organizations Struggle to Execute
Our research revealed a significant contradiction: while security remains a top priority for most organizations, many still face significant inefficiencies in their IAM practices. In interviews with IT leaders, security was repeatedly cited as a key concern. However, our quantitative data revealed that organizations often rely on a patchwork of authentication methods—an average of four across different applications. Despite this, 21% of respondents reported experiencing multiple security breaches over the past year.

This gap highlights a critical insight: while organizations believe they’re well-protected by multiple layers of security, they may still be vulnerable. Could your organization be operating under a false sense of security? It’s essential to assess whether your IAM strategy is truly up to the task in today’s threat landscape.
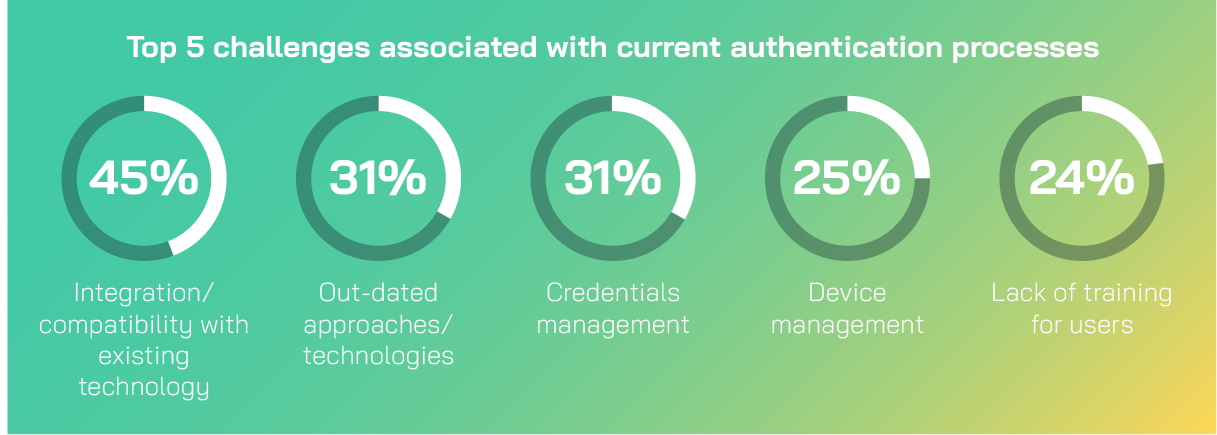
IAM Challenges: An Industry-Wide Issue
Nearly nine in ten (89%) organizations reported facing challenges with their current authentication methods. Many are still grappling with outdated technologies; 31% of respondents identified this as a key issue. This presents a prime opportunity for organizations to modernize their IAM systems and improve security posture.
The threats facing organizations are evolving rapidly, with cybercriminals becoming more sophisticated every day. Our research found that phishing (72%) and social engineering (62%) are the most common attack vectors in the identity management space, further emphasizing the need for stronger, more resilient IAM systems. Therefore, adopting robust, modern authentication methods is essential.
So what does the future hold for Identity and Access Management?
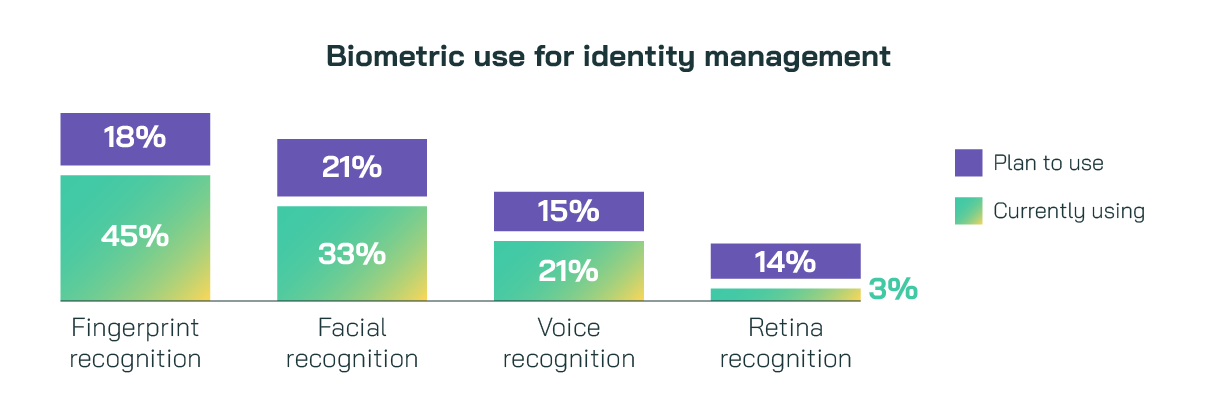
Looking ahead, our research points to passwordless authentication as a game-changer for the future of identity management. Biometric authentication, in particular, offers a powerful alternative to traditional passwords by leveraging unique physical characteristics to verify identity. Our findings show that nearly two-thirds (63%) of organizations are already using or plan to adopt fingerprint recognition. Fewer organizations are implementing facial recognition (45%) and voice recognition (36%), but the trend is clear—biometric solutions are becoming a cornerstone of IAM strategy.
Our qualitative interviews also revealed a growing interest in multi-modal authentication — combining several biometric methods for a more secure and user-friendly experience. This layered approach not only improves protection but also reduces the chances of false positives, ensuring a smoother, more reliable user experience.

Is your organization exploring these biometrics-based methods? If not, now may be the time to consider them as a critical step in strengthening your security infrastructure.
Methodology
100 IT decision makers from the Vanson Bourne Community were interviewed in the UK in June 2024. All came from organisations across a range of sizes and private and public sectors. As a member of the Vanson Bourne Community you’ll gain access exclusive to a variety of insights reports just like this one, based on research with our members. Sign up for free here.


